envbroker
[!NOTE] Are you worried your agent might do stupid stuff with your precious
.envvariables?
Do you handle high-risk secrets like wallet keys, API tokens, or service credentials in your.envfile while vibe-coding ?
envbroker is a CLI for guarding secret variables that usually live in .env files, such as API_KEY, SECRET_KEY, database URLs, and access tokens, while still making them available to approved commands.
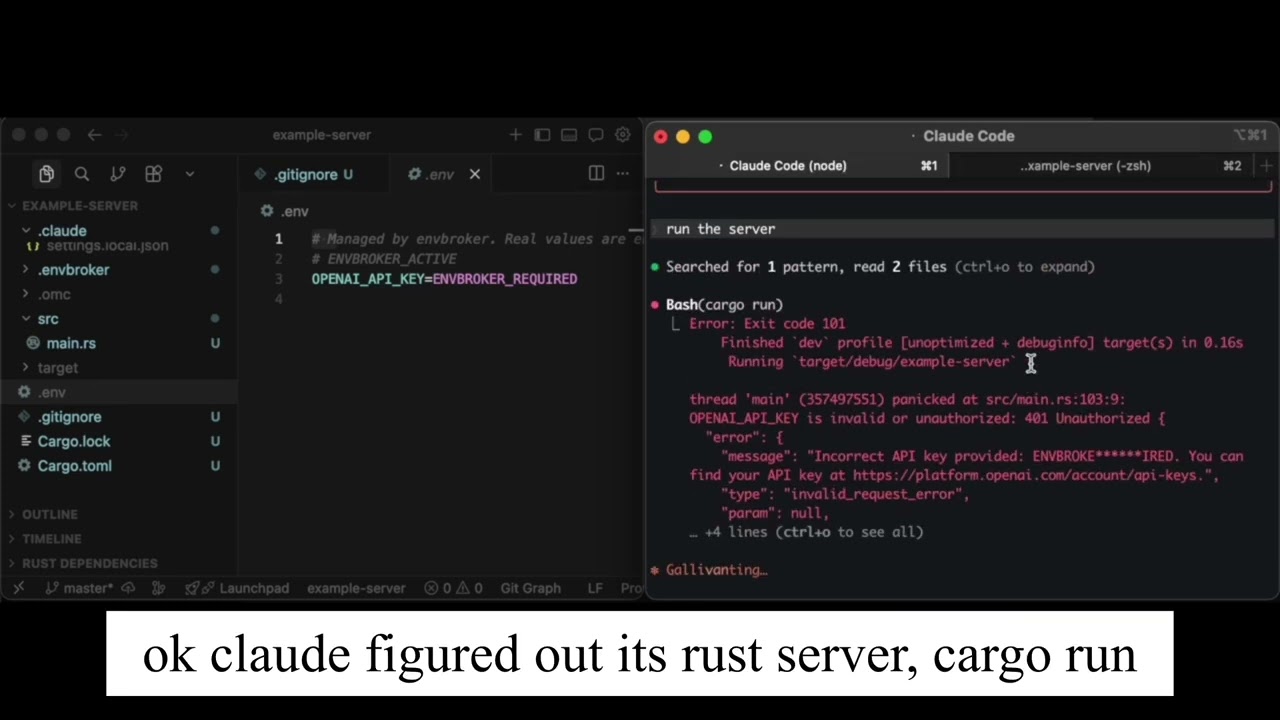
It is built for agentic coding workflows, especially high-autonomy or YOLO-style runs where an agent can move quickly and touch a lot of files and commands. Instead of relying on a fancy sandbox, envbroker uses a simple approach that works in practice: encrypt the real .env, store it outside the repository, replace the in-repo file with placeholders, and use Claude Code hooks to steer secret-dependent commands through envbroker run.
btw this cli is vibe coded also lol
Status
The current implementation focuses on:
- Claude Code integration
ageencryption for secret payloads- OS keychain storage for the decryption identity
- Git-repository workflows with placeholder
.envfiles
Demo
Installation
Quick Start
- Create a normal
.envin a git repository. - Install Claude Code integration.
- Run your secret-dependent commands through
envbroker run.
After installation, the original .env is rewritten to placeholders like this:
# Managed by envbroker. Real values are encrypted outside this repository.
# ENVBROKER_ACTIVE
OPENAI_API_KEY=ENVBROKER_REQUIRED
DATABASE_URL=ENVBROKER_REQUIRED
How It Works
envbroker install claudeparses your.env, encrypts it withage, stores the identity in the OS keychain, and writes ciphertext outside the repository..envis replaced withENVBROKER_REQUIREDplaceholders.- Claude Code hooks are installed:
- PreToolUse blocks direct
.envreads (cat .env, etc.) and prompts for approval onenvbroker runcommands. - PostToolUseFailure detects when a command fails due to placeholder values and guides Claude to retry through
envbroker run -- ....
- PreToolUse blocks direct
- You just prompt Claude normally. The hooks handle secret access automatically — no need to mention
.envorenvbrokerin your prompt.
Command Reference
envbroker install claude [--scope <local|project|user>] [--env-file <path>] [--profile <name>]
envbroker uninstall claude [--scope <local|project|user>]
envbroker run [--profile <name>] -- <command>...
envbroker status
envbroker doctor
envbroker list-vars [--profile <name>]
Useful examples:
Files and Data
In the repository:
.envbecomes a placeholder file.envbroker/config.jsonstores repo-local metadata.claude/hooks/envbroker-pretooluseand.claude/hooks/envbroker-posttoolusefailureare created- Claude settings are updated with a deny rule for
Read(./.env)and envbroker hook entries
Outside the repository:
- encrypted secrets are stored under the platform app-data directory for
envbroker - project metadata is stored alongside the encrypted payload
- the decryption identity is stored in the OS keychain under the
envbrokerservice
Caveats
- Run
envbrokerinside a git repository. Project discovery walks upward until it finds.git. - Current agent installation flow is Claude-specific.
- The repository code currently uses the Apple Keychain backend for
keyring.
Development
License
MIT. See LICENSE.