Crate matrix_sdk_crypto
source ·Expand description
A no-network-IO implementation of a state machine that handles E2EE for Matrix clients.
Usage
If you’re just trying to write a Matrix client or bot in Rust, you’re probably looking for matrix-sdk instead.
However, if you’re looking to add E2EE to an existing Matrix client or library, read on.
The state machine works in a push/pull manner:
- you push state changes and events retrieved from a Matrix homeserver /sync response into the state machine
- you pull requests that you’ll need to send back to the homeserver out of the state machine
use std::collections::BTreeMap;
use matrix_sdk_crypto::{EncryptionSyncChanges, OlmMachine, OlmError};
use ruma::{
api::client::sync::sync_events::{v3::ToDevice, DeviceLists},
device_id, user_id,
};
#[tokio::main]
async fn main() -> Result<(), OlmError> {
let alice = user_id!("@alice:example.org");
let machine = OlmMachine::new(&alice, device_id!("DEVICEID")).await;
let changed_devices = DeviceLists::default();
let one_time_key_counts = BTreeMap::default();
let unused_fallback_keys = Some(Vec::new());
let next_batch_token = "T0K3N".to_owned();
// Push changes that the server sent to us in a sync response.
let decrypted_to_device = machine.receive_sync_changes(EncryptionSyncChanges {
to_device_events: vec![],
changed_devices: &changed_devices,
one_time_keys_counts: &one_time_key_counts,
unused_fallback_keys: unused_fallback_keys.as_deref(),
next_batch_token: Some(next_batch_token),
}).await?;
// Pull requests that we need to send out.
let outgoing_requests = machine.outgoing_requests().await?;
// Send the requests here out and call machine.mark_request_as_sent().
Ok(())
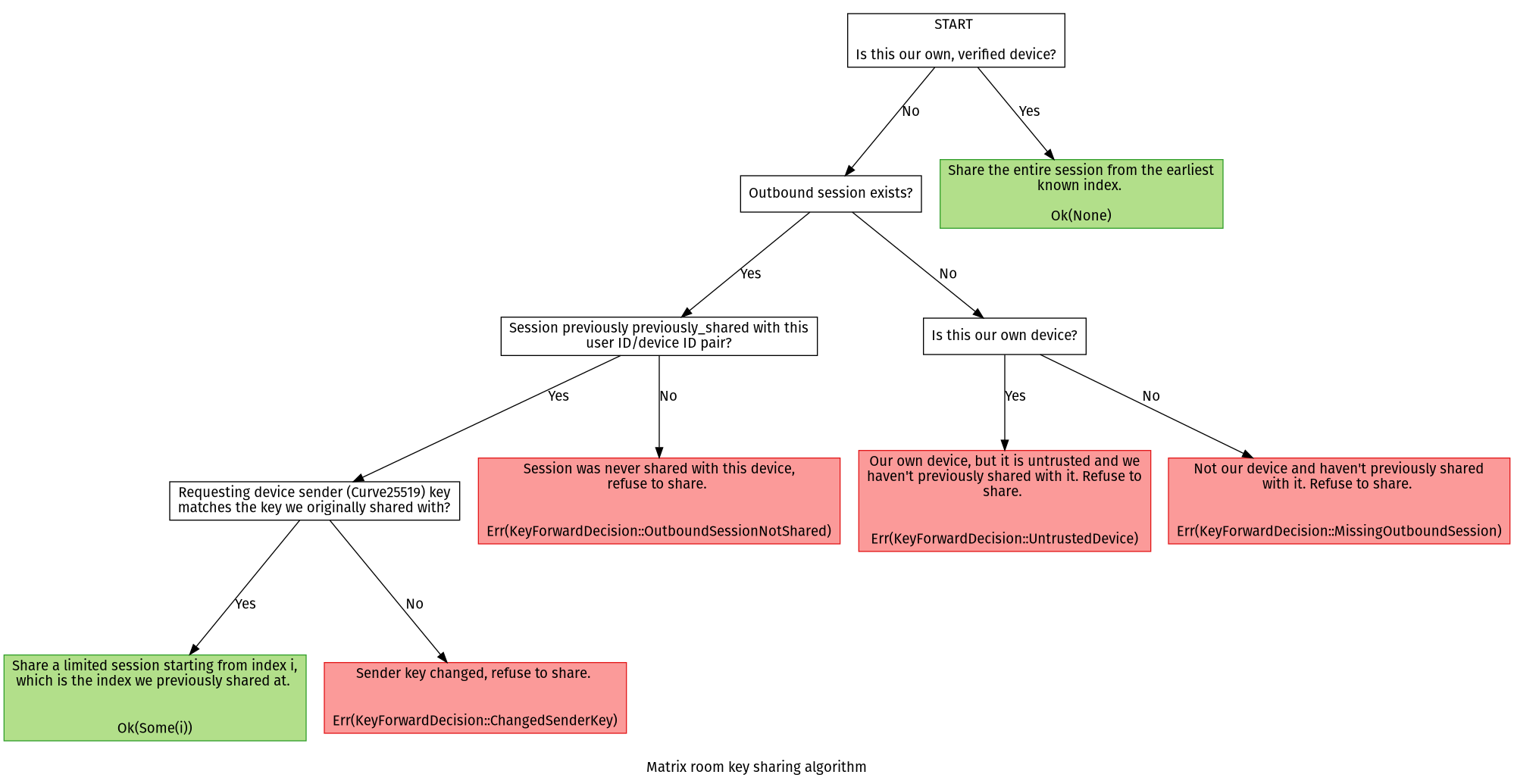
}Room key sharing algorithm
The decision tree below visualizes the way this crate decides whether a room key will be shared with a requester upon a key request.
Crate Feature Flags
The following crate feature flags are available:
-
qrcode: Enbles QRcode generation and reading code -
testing: provides facilities and functions for tests, in particular for integration testing store implementations. ATTENTION: do not ever use outside of tests, we do not provide any stability warantees on these, these are merely helpers. If you find you need any function provided here outside of tests, please open a Github Issue and inform us about your use case for us to consider.
Re-exports
pub use olm::Account;pub use olm::CrossSigningStatus;pub use olm::EncryptionSettings;pub use olm::Session;pub use requests::IncomingResponse;pub use requests::KeysBackupRequest;pub use requests::KeysQueryRequest;pub use requests::OutgoingRequest;pub use requests::OutgoingRequests;pub use requests::OutgoingVerificationRequest;pub use requests::RoomMessageRequest;pub use requests::ToDeviceRequest;pub use requests::UploadSigningKeysRequest;pub use store::CrossSigningKeyExport;pub use store::CryptoStoreError;pub use store::SecretImportError;pub use store::SecretInfo;pub use store::TrackedUser;pub use vodozemac;
Modules
- Server-side backup support for room keys
- Submodule for device dehydration support.
- The crypto specific Olm objects.
- Modules containing customized request types.
- Helpers for implementing the Secrets Storage mechanism from the Matrix spec.
- Types and traits to implement the storage layer for the
OlmMachine - Module containing customized types modeling Matrix keys and events.
Structs
- Customize the accept-reply for a verification process
- Struct containing the protocols that were agreed to be used for the SAS flow.
- A wrapper that transparently encrypts anything that implements
Readas an Matrix attachment. - A wrapper that transparently encrypts anything that implements
Read. - Information about the cancellation of a verification request or verification flow.
- A set of requests to be executed when bootstrapping cross-signing using
OlmMachine::bootstrap_cross_signing. - A device represents a E2EE capable client of an user.
- An emoji that is used for interactive verification using a short auth string.
- The short auth string for the emoji method of SAS verification.
- Data contained from a sync response and that needs to be processed by the OlmMachine.
- A struct describing an outgoing key request.
- Struct containing a
m.secret.sendevent and its acompanying info. - Struct holding all the information that is needed to decrypt an encrypted file.
- State machine implementation of the Olm/Megolm encryption protocol used for Matrix end to end encryption.
- Struct representing a cross signing identity of a user.
- A read-only version of a
Device. - Struct representing a cross signing identity of our own user.
- Struct representing a cross signing identity of a user.
- Return type for the room key importing.
- Short authentication string object.
- A read only view over all devices belonging to a user.
- Struct representing a cross signing identity of a user.
- An object controlling key verification requests.
Enums
- Error type for attachment decryption.
- Error that occurs when decrypting an event that is malformed.
- Error representing a failure during key export or import.
- The local trust state of a device.
- Error representing a failure during a group encryption operation.
- Error representing a failure during a device to device cryptographic operation.
- Enum over the different user identity types we can have.
- An Enum describing the state the SAS verification is in.
- Error that occurs when a room key can’t be converted into a valid Megolm session.
- Error type describing different errors that happen when we check or create signatures for a Matrix JSON object.
- Enum over the different user identity types we can have.
- An enum over the different verification types the SDK supports.
- An Enum describing the state the verification request is in.
Statics
- The version of the matrix-sdk-cypto crate being used
Functions
- Try to decrypt a reader into a list of exported room keys.
- Encrypt the list of exported room keys using the given passphrase.
- Format the list of emojis as a two line string.